Digital Security Systems
Cameras

AKEA video analytics offer complete, in-depth solutions for customising your video capture needs to particular, relevant-only data that delivers extensive threat analysis notification to security employees. Our solutions allow you to record in real time, specify particular regions, detect licence plates or vehicle features, recognise faces, and record events preceding a given movement.
Storage
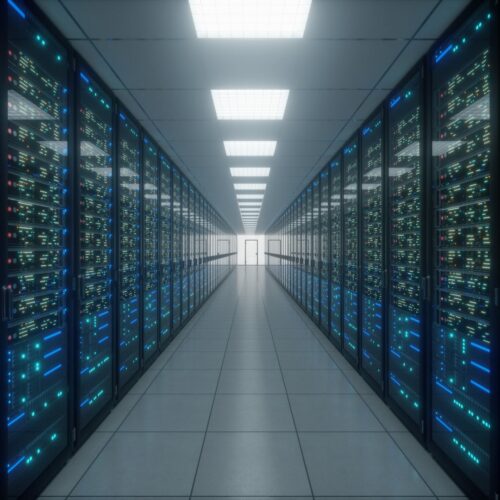
Our engineers create cost-effective, scalable network attached storage solutions that include: reduced resource requirements for system maintenance personnel, a single centralised digital video processor, cost-effective green solutions, and fully and simplified scalability for escalating expansion and growth needs.
Access Control/Security

We offer low-cost turnkey Access Control Systems that are tailored to your unique needs for granting authorization to regulate access to regions and resources within a physical facility or computer-based information system. Personnel tracking, picture verification, employee information, and event recording may all be provided through Managed Access Control.
Visitor Mgmt System

AKEA's Visitor Management services allow it to precisely, effectively, and covertly track the use of a public facility or site. Visitors entering a 'secure' building, facility, or campus in many companies can acquire access by merely signing their name in a visitor log book.
Computer Visitor Management Systems

Simple electronic visitor management systems monitor and record visitor information over a computer network. More advanced systems include picture ID, database searching, automated door entry, and other features.
Visitor Management Software

There are a number of desktop-based visitor management software programmes available. These apps usually include three main components: visitor registration, visitor badge printing, and reporting capabilities.
Card
Access

By the use of three forms of authenticating information, electronic access control overcomes the constraints of mechanical locks and keys. Keypads that need a password or a code. Smart cards or proximity cards are examples of access cards. Biometrics, such as fingerprint or face recognition, are validated by biometric measurement.
Our Approach and Benefits

Our security Engineering team creates a cost-effective system for all budgets that allows for future development and expansion as well as updating, whether it's a classic analogue system or a full IP-based system.
How We Work

We obtain the project's location, as well as the site's solar irradiance.
Determines the tilt angle for optimal solar energy gathering. Support Structures are chosen.

Computes the yearly solar generation. Determines the size of the system necessary by identifying the week months.
We proceed with comprehensive engineering, in which minute factors are addressed and the system is optimised.
The project components are manufactured after extensive engineering.

Components are tested in accordance with the designs and applicable standards, assuring quality, quantity, performance, and safety.
All of the components are delivered to the job site and assembled.
After assembly, the system is commissioned and its performance is reviewed.
Connect Us
Have a project to discuss with us?